Mission-critical advisory to mitigate vulnerabilities, improve resilience, and outmaneuver adversarial tactics across multi-domain environments.
575+
Successful Projects
99%
Customer satisfaction

We conduct a comprehensive analysis of your operational terrain, identifying critical vulnerabilities and threat vectors.
We develop tailored countermeasures and operational safeguards based on adversarial emulation and threat modeling.
We Provide in-depth training, briefings, and actionable recommendations to give your team with the tools to maintain a robust security posture.
We offer ongoing consultation to adapt to evolving threats and ensure sustained operational effectiveness.
// Our services //
Gain insights into adversarial tactics, techniques, and procedures (TTPs) to inform your operational strategy.
Learn More →
Identify and mitigate critical vulnerabilities in your systems and applications.
Learn More →
Develop tailored strategies to assess, prioritize, and mitigate risks.
Learn More →
Empower your team with advanced OPSEC techniques to protect sensitive information.
Learn More →
Craft comprehensive frameworks and guidelines to align with objectives.
Learn More →
Implement proactive measures to detect, neutralize, and prevent malware threats.
Learn More →
Rapidly detect, contain, and recover from cyber incidents to minimize operational disruption.
Learn More →
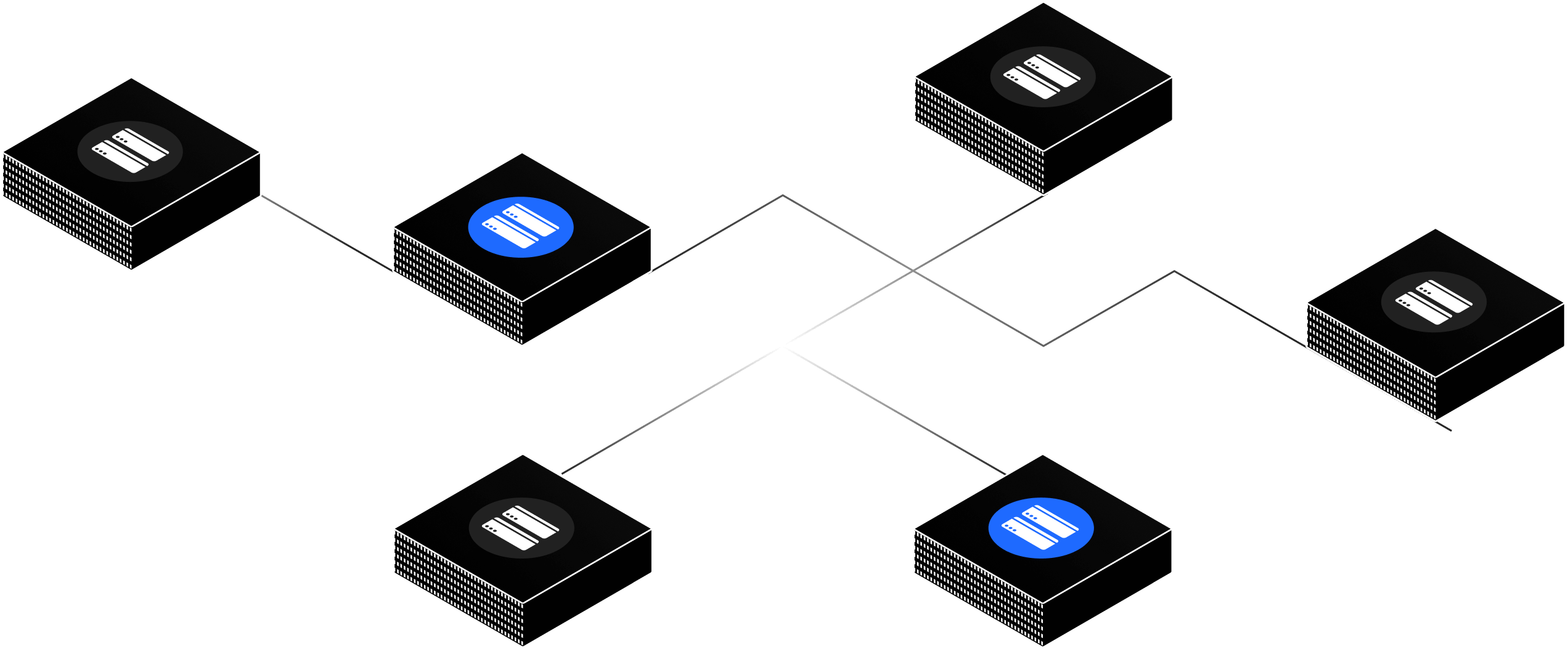
Streamline your security operations with automated tools and workflows in real time.
Learn More →
You need to be a logged-in member to view articles.